Supercomputer architecture
A supercomputer is a computer architecture designed to maximize calculation speed. This in contrast with a mainframe, which is optimized for high I/O throughput. Supercomputers are the fastest machines available at any given time. Since computing speed increases continuously, supercomputers are superseded by new supercomputers all the time.
Supercomputers are used for many tasks, from weather forecast calculations to the rendering of movies like Toy Story and Shrek.
Originally, supercomputers were produced primarily by a company named Cray Research. The Cray-1 was a major success when it was released in 1976. It was faster than all other computers at the time and it went on to become one of the best known and most successful supercomputers in history. The machine cost $8.9 million when introduced.
Cray supercomputers used specially designed CPUs for performing calculations on large sets of data. Together with dedicated hardware for certain instructions (like multiply and divide) this increased performance.
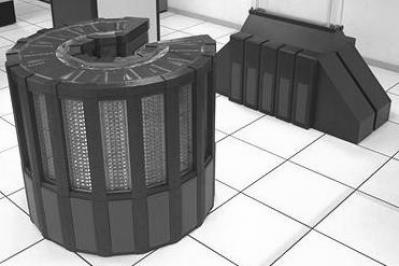
The entire chassis of the Cray supercomputers was bent into a large C-shape. Speed-dependent portions of the system were placed on the "inside edge" of the chassis where the wire-lengths were shorter to decrease delays. The system could peak at 250 MFLOPS (Million Floating Point Operations per second).
In 1985, the very advanced Cray-2 was released, capable of 1.9 billion floating point operations per second (GFLOPS) peak performance, almost eight times as much as the Cray-1. In comparison, in 2015, the Intel Core i7 5960X CPU has a peak performance of 354 GFLOPS ; more than 185 times faster than the Cray-2!
Supercomputers as single machines started to disappear in the 1990s. Their work was taken over by clustered computers – a large number of off-the-shelf x86 based servers, connected by fast networks to form one large computer array. Nowadays high performance computing is done mainly with large arrays of x86 systems. In 2015, the fastest computer array was a cluster with more than 3,120,000 CPU cores, calculating at 54,902,400 GFLOPS, running Linux .
In some cases specialized hardware is used to realize high performance. For example, graphics processors (GPUs) can be used for fast vector based calculations and Intel CPUs now contain special instructions to speed up AES encryption.
In 2015, the NVidia's Tesla GPU PCIe card (basically a graphics card but without a graphics connector) provides hundreds of vector based computing cores and more than 8,000 GFLOPS of computing power . Four of these cards can be combined in one system for extremely high performance calculations, for just a fraction of the cost of traditional supercomputers.
This entry was posted on Friday 11 December 2015
 English
English