Desktop virtualization
A number of virtualization technologies can be deployed for end user devices. Application virtualization can be used to run applications on an underlying virtualized operating system. And instead of running applications on end user devices themselves, using a thin client, applications can also be run on virtualized PCs based on Server Based Computing (SBC) or Virtual Desktop Infrastructure (VDI). All of these technologies are explained in the next sections.
Application virtualization
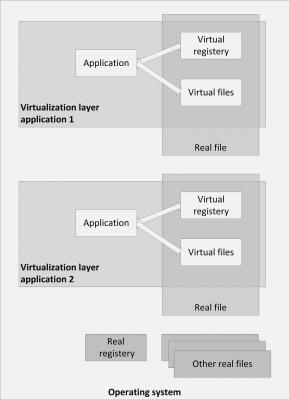
The term application virtualization is a bit misleading, as the application itself is not virtualized, but the operating system resources the application uses are virtualized. Application virtualization isolates applications from some resources of the underlying operating system and from other applications, to increase compatibility and manageability.
The application is fooled into believing that it is directly interfacing with the original operating system and all the resources managed by it. But in reality the application virtualization layer provides the application with virtualized parts of the runtime environment normally provided by the operating system.
Application virtualization is typically implemented in a Windows based environment
The application virtualization layer proxies all requests to the operating system and intercepts all file and registry operations of the virtualized applications. These operations are transparently redirected to a virtualized location, often a single real file.
Since the application is now working with one file instead of many files and registry entries spread throughout the system, it becomes easy to run the application on a different computer, and previously incompatible applications or application versions can be run side-by-side.
Examples of application virtualization products are Microsoft App-V and VMware ThinApp.
Server Based Computing
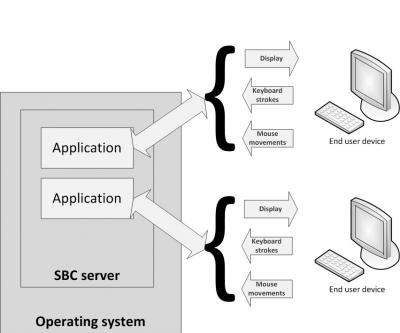
Server Based Computing (SBC) is a concept where applications and/or desktops running on remote servers relay their virtual display to the user's device. The user’s device runs a relatively lightweight application (a thin client agent) that displays the video output and that fetches the keyboard strokes and mouse movements, sending them to the application on the remote server. The keyboard and mouse information is processed by the application on the server, and the resulting display changes are sent back to the user device.
SBC requires a limited amount of network bandwidth, because only changed display information is sent to the end user device and only keyboard strokes and mouse movements are sent to the server.
SBC is typically implemented in a Windows based environment, where the SBC server is either Windows Remote Desktop Service (RDS, formerly known as Windows Terminal Services) or Citrix XenApp (formerly known as MetaFrame Presentation Server). XenApp provides more functionality than RDS, but is a separate product, whereas RDS is part of the Windows operating system.
A big advantage of using SBC is that maintenance (like applying patches and upgrades) can be done at the server level. The changes are available instantly to all users – freeing systems managers of managing a large set of PC deployments.
With SBC, server-side CPU and RAM capacity is shared with applications from all users. Extensive use of CPU and/or RAM in one user's session can influence the performance of sessions of other users on the same server.
Application configurations are the same for all users and use the graphical properties of the SBC server instead of that of the client end user device.
Limitations on the desktop experience (slow response or keyboard lag) are mostly due to network latency or the configuration of the remote desktop. In most cases security and stability settings (protecting changes to shared resources) could also influence the experience. With a good configuration of the roaming user profile, folder redirection for network storage of user data, and the latest application virtualization techniques, limitations in desktop usage can be minimal.
Virtual Desktop Infrastructure (VDI)
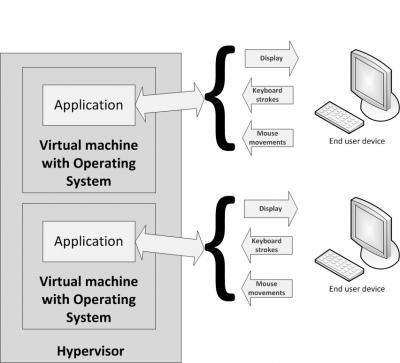
Virtual Desktop Infrastructure (VDI) is a similar concept as SBC, only in VDI user applications run in their own virtual machine.
VDI utilizes a virtual desktop running on top of a hypervisor, typically VMware View, Citrix XenDesktop, or Microsoft MED-V. The hypervisor's primary task is to distribute the available hardware resources between the virtual machines hosted on the physical machine.
Just like with a physical PC, with VDI, each user has exclusive use of the operating system, CPU, and RAM, whereas with SBC users share these resources. VDI enables applications and operating systems to run next to each other in complete isolation without interference.
Protocols supported to exchange video, keyboard, and mouse from client to virtual machine are the ICA (Independent Computing Architecture) protocol of Citrix, Microsoft’s RDP (Remote Desktop Protocol), and the VMware PCoIP protocol.
VDI tends not to scale well in terms of CPU resources and storage IOPS, because each client uses an entire virtual machine. Booting a system leads to much I/O to the server. A so-called 'Logon storm' occurs when a lot of virtualized systems boot up at the same time. These logon storms can partly be prevented by pre-starting a predefined number of virtual machines at configured time slots.
Thin clients
VDI and SBC both enable the hosting of desktops on central server farms and use the same protocols to deliver the output of application screens to users. Thin clients communicate with the SBC or VDI server. They come in two flavors: hardware and software based thin clients.
Hardware based thin clients are lightweight computers that are relatively inexpensive and have no moving parts nor local disk drives. The devices have no configuration and can be used directly after plugging them into the network, making it easy to replace when one fails. They eliminate the requirement for upgrading PCs or laptops on a regular basis.
Software based thin clients are applications running in a normal client operating system like Windows, Linux, or Mac OS X. They can also run on mobile devices like tablets and smartphones.
This entry was posted on Vrijdag 27 November 2015
 English
English