IP Protocol (IPv4) classes and subnets
IPv4 addresses are composed of 4 bytes (32 bits), represented by 4 decimal numbers, for example, 192.168.1.1. Each host (server, switch, router, firewall, etc.) in the IP network needs at least one IP address. Within a network all IP addresses must be unique.
An IP address consists of two fields, a network prefix and a host number. For instance, in the IP address 10.121.12.16, the network prefix is 10 and the host number is 121.12.16.

All hosts in the same network can communicate directly to each other. Hosts in other networks can only be reached using a router. For example, consider the following three hosts:
Host A IP address: 192. 168. 1. 1
with subnet mask: 255. 255. 255. 0
is in network: 192. 168. 1. 0
with broadcast address 192. 168. 1. 255
and is host number 1 in that network
Host B IP address: 192. 168. 3. 4
with subnet mask: 255. 255. 255. 0
is in network: 192. 168. 3. 0
with broadcast address 192. 168. 3. 255
and is host number 4 in that network
Host C IP address: 192. 168. 3. 8
with subnet mask: 255. 255. 255. 0
is in network: 192. 168. 3. 0
with broadcast address 192. 168. 3. 255
and is host number 8 in that network
To have host B (192.168.3.4) and C (192.168.3.8) communicating with each other no routing is needed since both hosts are in the same network (192.168.3.0).
To have host A (192.168.1.1) and B (192.168.3.4) communicating with each other, however, a router must be setup to route packets between networks 192.168.1.0 and 192.168.3.0. It is important to note that routers route packets between networks (sets of IP addresses) and do not route between individual IP addresses.
The first three bits of the first byte of an IP address define the class of the address. Three classes of networks are defined:
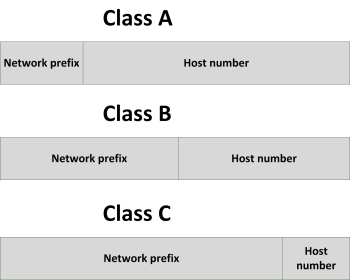
In a typical class C address like 195.23.221.23, the network is 195.23.221 and the host number is 23.
|
Class |
First byte |
Max number of hosts |
Number of available networks |
|
A |
0–127 |
16,777,214 |
128 |
|
B |
128–191 |
65,534 |
16,384 |
|
C |
192–223 |
254 |
2,097,152 |
This means that the IP address 170.32.43.12 is a class B network. This network can have 65,534 hosts in it. The problem is that there are only 16,384 class B networks available worldwide, and only 128 class A networks. Only very large companies (like IBM) and some governments own a class A network, all other organizations sometimes use a class B, and mostly use a class C network.
Classful network design served its purpose in the startup stage of the Internet, but it lacked scalability in the face of the rapid expansion of the network in the 1990s. For instance, when an organization only needs five hosts in their network, they needed to get a class C network, even if they used only five of its 254 available host addresses.
To solve the problem of this inefficient use of IP addresses the class system of the address space was replaced with Classless Inter-Domain Routing (CIDR) in 1993. CIDR is based on variable-length subnet masking (VLSM) to allow allocation and routing based on arbitrary-length prefixes. This system is also known as subnetting.
Subnetting
Subnetting is used to split up the host part of an IP network in smaller subnets, each forming a new IP network. Consider the following example:
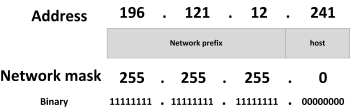
In this case, the IP address 196.121.12.241 has a network prefix of 196.121.12 and a host number of 241 (in the host range between 1 and 254).
For IPv4 a network mask is a 32-bit number (expressed in four decimals) where bits set to 1 signify the network prefix and bits set to 0 the host part of the address. Essentially to get the network address from an IP address the IP address and the subnet mask are ANDed together, to get the host part the IP address and the negated subnet mask are ANDed together. The default subnet mask of a class C network is 255.255.255.0.
As an alternative, the routing prefix can also be expressed in Classless Inter-Domain Routing (CIDR) notation. It is written as the address of a network, followed by a slash character (/), and ending with the bit-length of the host space. For example, 255.255.255.0 is the network mask for the 192.168.1.0/24 notation.
Now consider the following example using a subnet:
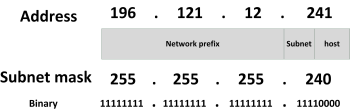
In this case, the IP address 196.121.12.129 has a network prefix of 196.121.12, a subnet of 240 and a host number of 1 (in the host range between 1 and 14).
Using subnets, the available IP address space can be used much more efficiently, as unused host addresses are simply not reserved or wasted. In the next table, the number of hosts that can be used is shown for certain subnet masks.
|
CIDR prefix |
Subnet mask |
Available subnets |
Hosts per subnet |
|
/24 |
255.255.255.0 |
1 |
254 |
|
/25 |
255.255.255.128 |
2 |
126 |
|
/26 |
255.255.255.192 |
4 |
62 |
|
/27 |
255.255.255.224 |
8 |
30 |
|
/28 |
255.255.255.240 |
16 |
14 |
|
/29 |
255.255.255.248 |
32 |
6 |
|
/30 |
255.255.255.252 |
64 |
2 |
|
/31 |
255.255.255.254 |
128 |
2 (only point-to-point) |
To directly connect two routers with each other, a subnet with 4 addresses is needed (each router needs one IP address, plus the subnet needs a broadcast address and a network address), leading to a subnet mask of 255.255.255.252. Point/to/point connections need no broadcast or network address and can use a subnet mask of 255.255.255.254.
Using subnets allows Internet Service Providers to for instance provide 32 organizations with six public IP addresses each and only using one class C IP network for it.
To maximize the number of IP addresses available in the various LAN segments in an internal network and to minimize the size of routing tables in routers, a well-designed IP addressing plan is needed. In such an addressing plan the available IP ranges are divided in various subnets, each with its own set of users.
Private IP ranges
Since the number of unique IP addresses on the Internet is limited and because hosts with public Internet IP addresses can reach the internet directly, private IP addresses should be used for LANs instead. The following IPv4 address ranges can be used for internal use – so-called private IP address ranges:
- 10.0.0.0 to 10.255.255.255 (class A address range)
- 172.16.0.0 to 172.31.255.255 (class B address range)
- 192.168.0.0 to 192.168.255.255 (class C address range)
These IP addresses are not used on the Internet and by default they are not routed by Internet routers. This means each organization can use these IP ranges internally without introducing conflicts on the Internet. It is a good practice to create separate subnets within the chosen address range for:
- Production environment workstations
- Production environment servers
- Office environment workstations
- Office environment servers
- Development and test environments
- De-Militarized Zone
- Systems management network segment
- Printers
- Remote users
- Server clusters
- Guest users’ workstations
Routing between these subnets should be done using routers with access-lists, to block undesired network traffic.
This entry was posted on Vrijdag 07 December 2012
 English
English